Secure Web Infrastructure 900510042 plays a critical role in maintaining stability within digital environments. Its implementation of advanced encryption protocols and strict access controls ensures that sensitive information remains protected. Moreover, this infrastructure actively counters cyber threats while enabling ongoing risk management. Understanding its key features and best practices is essential for organizations aiming to strengthen their operational framework. However, the complexities of achieving optimal security may raise further questions about its effectiveness.
Understanding Secure Web Infrastructure 900510042
Understanding the concept of secure web infrastructure is essential for organizations aiming to maintain stability in their online operations.
A robust web architecture, complemented by effective data encryption protocols, safeguards sensitive information and enhances user trust.
This strategic approach ensures resilience against cyber threats, thereby fostering an environment where freedom of expression and secure transactions can coexist, ultimately supporting organizational objectives in an increasingly digital landscape.
Key Features That Enhance Stability and Security
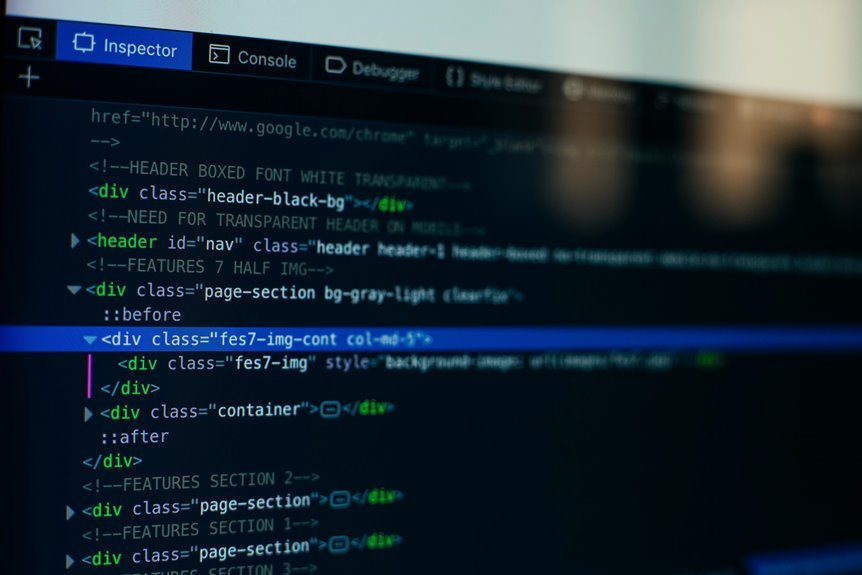
A secure web infrastructure encompasses several key features that significantly contribute to both stability and security.
Essential elements include robust encryption protocols that safeguard data during transmission, ensuring confidentiality and integrity.
Additionally, stringent access controls regulate user permissions, mitigating unauthorized access risks.
Together, these features create a resilient framework that empowers users with the freedom to navigate online environments securely and confidently.
How Does Secure Web Infrastructure Mitigate Cyber Threats?
While cyber threats continue to evolve in sophistication, a secure web infrastructure plays a pivotal role in mitigating these risks through a multifaceted approach.
Best Practices for Implementing Secure Web Infrastructure
To effectively implement secure web infrastructure, organizations must adopt a comprehensive strategy that encompasses various best practices tailored to their specific needs and threats.
Utilizing secure protocols, such as HTTPS and TLS, is essential for safeguarding data transmission.
Additionally, robust data encryption methods protect sensitive information at rest and in transit, ensuring that unauthorized access is minimized while maintaining user privacy and trust.
Conclusion
In conclusion, the implementation of Secure Web Infrastructure 900510042 stands as a pivotal measure in safeguarding digital environments. As organizations navigate an increasingly complex landscape of cyber threats, the stakes are high. Will they prioritize robust encryption and stringent access controls, or risk compromising sensitive data? The choice is clear; embracing this infrastructure not only enhances stability but also fortifies user trust. As the digital realm evolves, the question remains: can organizations afford to overlook such a critical framework?